Training to Train?
Several years ago, the United States Army published something that many of us had just been thinking about for years. Their article illustrated that there is a significant difference between “training to train”, and “training to task”.
So much of our training these days in law enforcement and private organizations is driven by litigation. That is, the fear that if we don’t demonstrate acceptable amounts of the appropriate training, we could fail a regulatory audit or get sued. So, as a response to this problem, we “train so that we can say that we were trained” according to a particular standard (e.g. ethics training, Sarbanes-Oxley, sexual harassment training etc).
On the other hand, training that drills down specific needs, techniques and protocols, that must one day be used to accomplish an important task (e.g. save a life) by the person who learned it, is known as “Training to task”. In other words, the student knows throughout the class, that they will soon have to perform the skills being taught in a competent manner. And one of the hazards we found in this type of presentation is that if students don’t recognize an
# ESI was and remains the most comprehensive with college-level distance learning followed by a fifteen day resident program.
# I once arrested an individual for theft, who listed as his occupation, “Bodyguard for the XXXX [musical group]”. When I checked his record I found he was a recently paroled felon, but he had in fact been employed as a bodyguard for the referenced group, prior to and after incarceration.
application for the material being presented, that they will “turn off” and the content will be ignored or rejected. Thus, it becomes increasingly important to identify at the beginning of the program, what the student’s personal and organizational goals are. They will absorb what they feel is relevant; thereby reinforcing the need to identify up front the type of knowledge and skills that will be relevant to their career path.
In our survey of protection training, we found that most schools offered as core elements, basic information or practical exercises relating to:
Advance work
Detail formations
Motorcades
Threat assessment
Hard skills (driving, shooting, DT)
Etiquette
Case studies/historical analysis of AOP’s
Bomb/IED/WMD recognition and mitigation
First Aid/CPR/AED
Physical and electronic security
Legal requirements
Communications/Command Post Ops
“Gear”
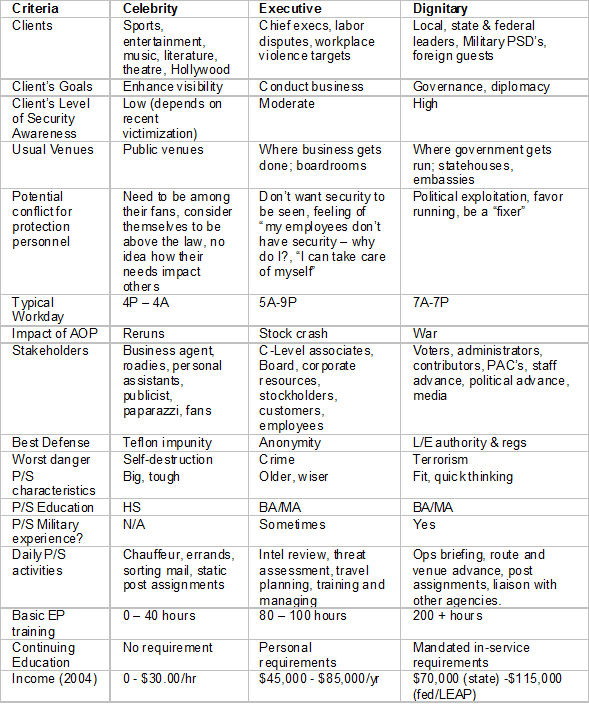
While we agreed that all of these subjects were valuable for the protection specialist, the specific type of work they were individually assigned might require far more emphasis on some subjects more than others. For instance, if there are only two people on your detail is it important for them to practice the six-man box formation? In reality, if you only have two agents, one will work the protectee and one should be on the advance, giving you “eyes and ears” at your next venue. If you think you will need both agents to counter a perceived or identified threat, then you probably need more than two.
If the protectee is a Fortune 100 CEO from Cedar Rapids who never interfaces with public figures, does it make sense to spend time on motorcade planning and assignment? If it is a one-person detail, you will probably use a contract driver, and if your advance has been thorough, you shouldn’t have to smash through any cars or execute any “J-Turns”.
Still, this is the kind of training that has sex-appeal for people just starting out in the business. The “hard skills” are what sells seats. We once offered a one-day seminar on “Conducting International Advances”, and only had one person sign up. The next month, we scheduled a “DT for Protection Specialists” and had a sell-out class; bringing us to the concept of “Enter-trainment”.
We found that most of the students who enroll in protection courses have a certain energy level that must be taxed in order for them to absorb the important components of the course. If you don’t make it enjoyable and high-energy, you will lose them before the first coffee break. But, how “high-energy” can the study of travel itineraries be? How exciting is it to study various transmission media used in the installation of residential and commercial intrusion systems?
Part three: 2/23/2009
I would like to know how to get started being a bodyguard.